AWS temporary credential best practice for developer access - console setup
Background
I've seen numerous posts on Reddit about people getting hacked or their access keys leaked. So I started this blog to address the gap in the issue. While AWS launched AWS SSO in 2017, not a lot of people are aware of it and most of the time people still resort to using IAM Users or worse the root account for day to day operations.
Do note that this just improves security, making it harder for attackers to get access and is not a foolproof method to make your account unhackable. You can still get hacked in numerous ways like exposing your access key(it will still be valid up to 1 hour after you first generated it, if you use the default value) or setting a weak root/sso user password with no MFA and many more like granting a random person IAM role access etc. The attack surface is limitless so please still be careful.
Let's start, I am unsure of the level of this blog. But personally, I would put it at level 200.
If you want a semi-automated setup with terraform script, please refer to this blog post
Prerequisite
- an AWS Account
Steps
Initial setup
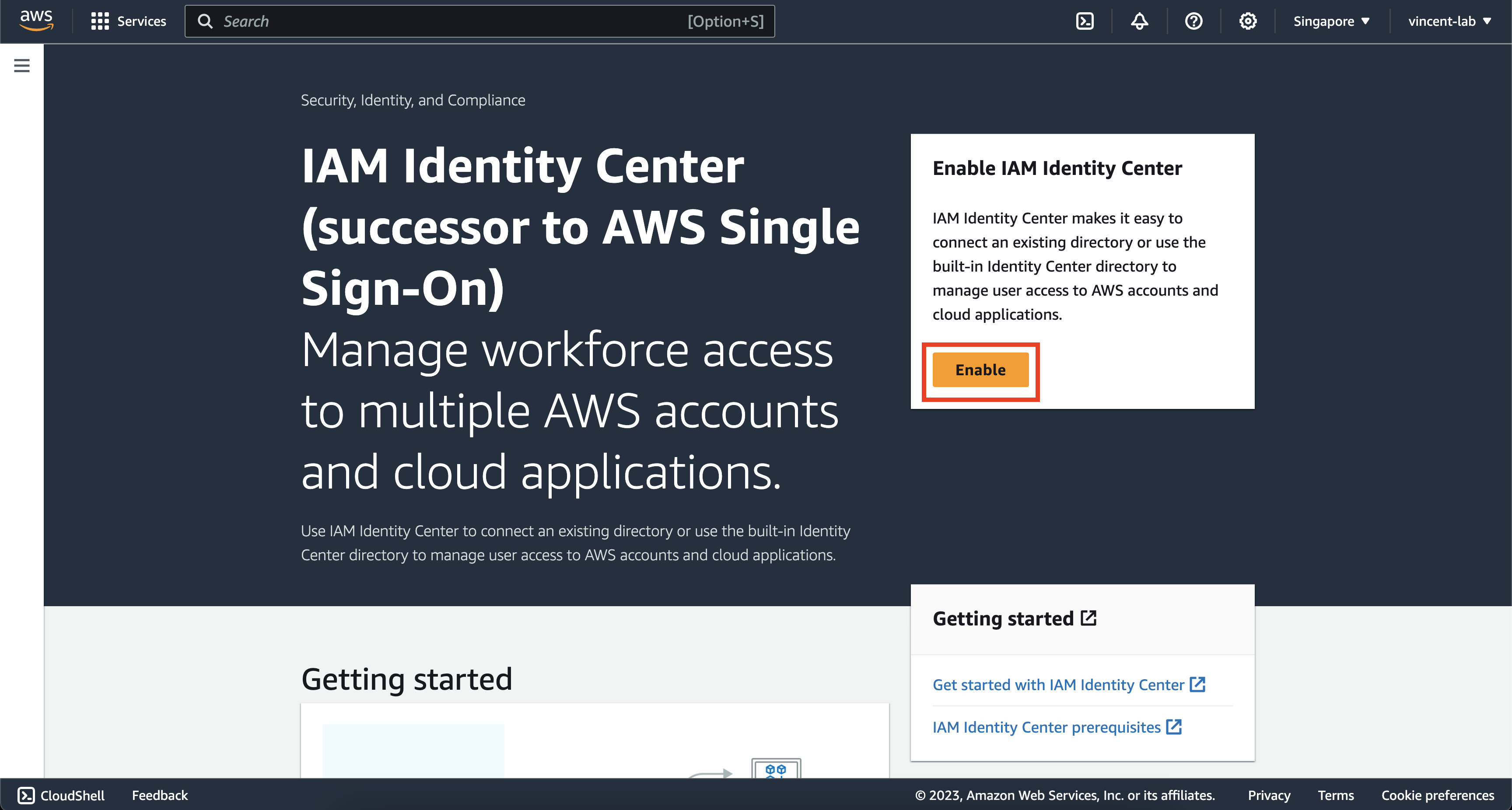
Go to https://console.aws.amazon.com/singlesignon/home on your AWS console then make sure that you have chosen the AWS region that is closest to you, for this example, I will be using the ap-southeast-1 region.
Go ahead and click Enable
Depending on whether you have enabled AWS Organization or not. You may or may not get this message. But if you do, click on Create AWS organization

Before continuing to create users, groups and permission sets. You will need to define some setup through the console. Unfortunately at the time of writing this blog AWS did not provide any API to enable these settings, so these steps must be done manually, I will probably be updating this guide when it's available.
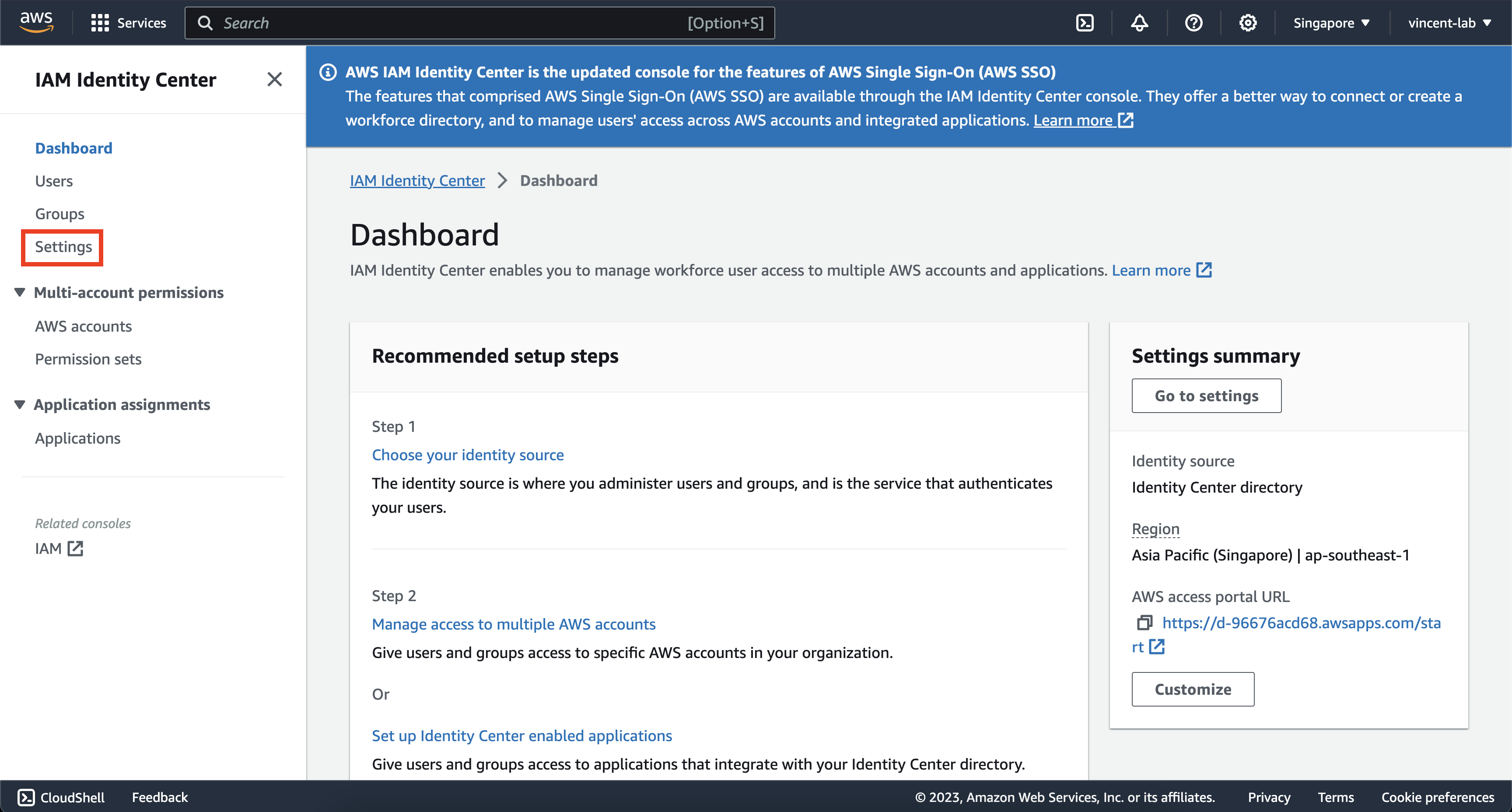
On your IAM Identity Center dashboard, click on settings on the left navigation bar
Click on Authentication
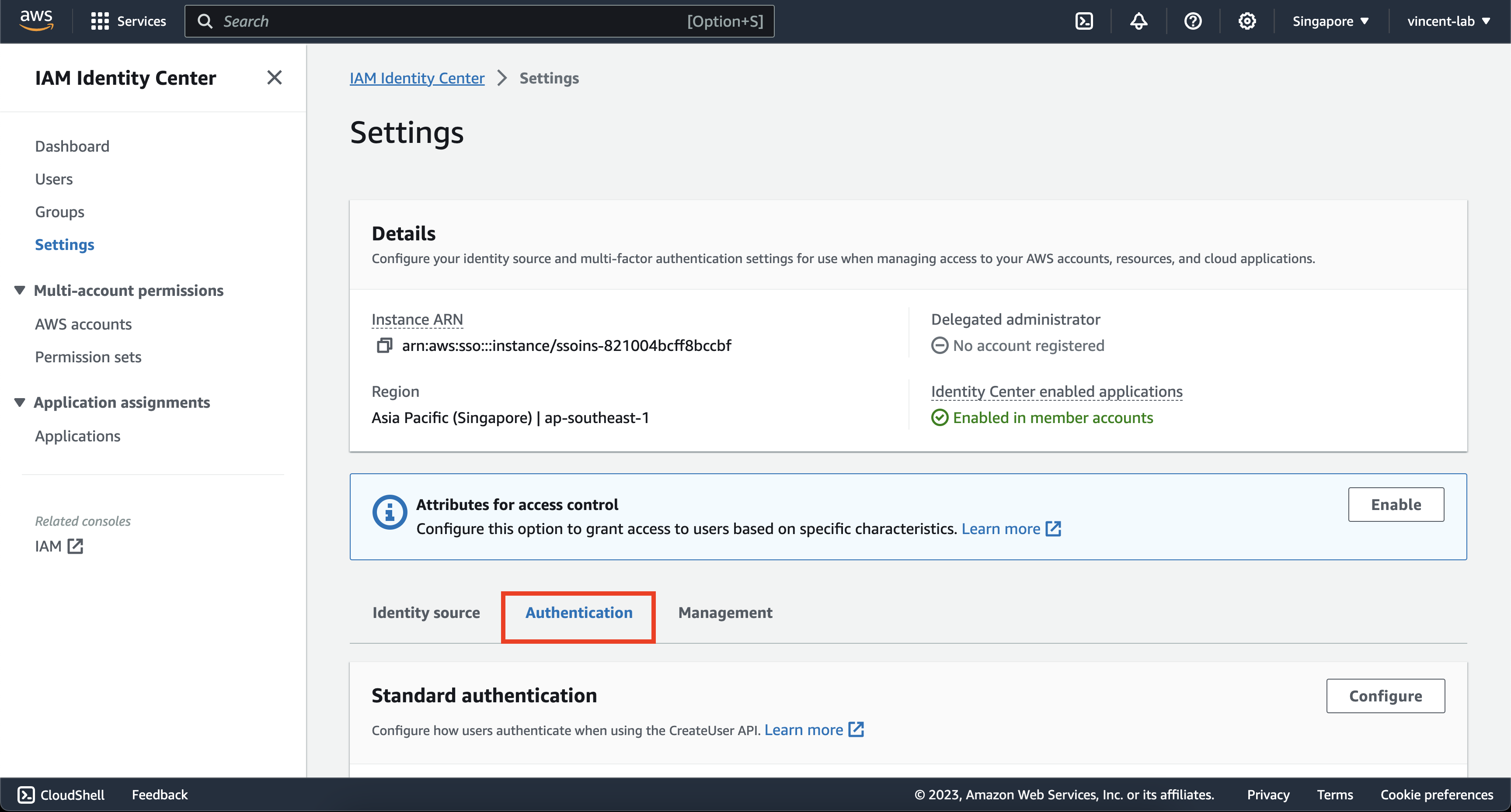
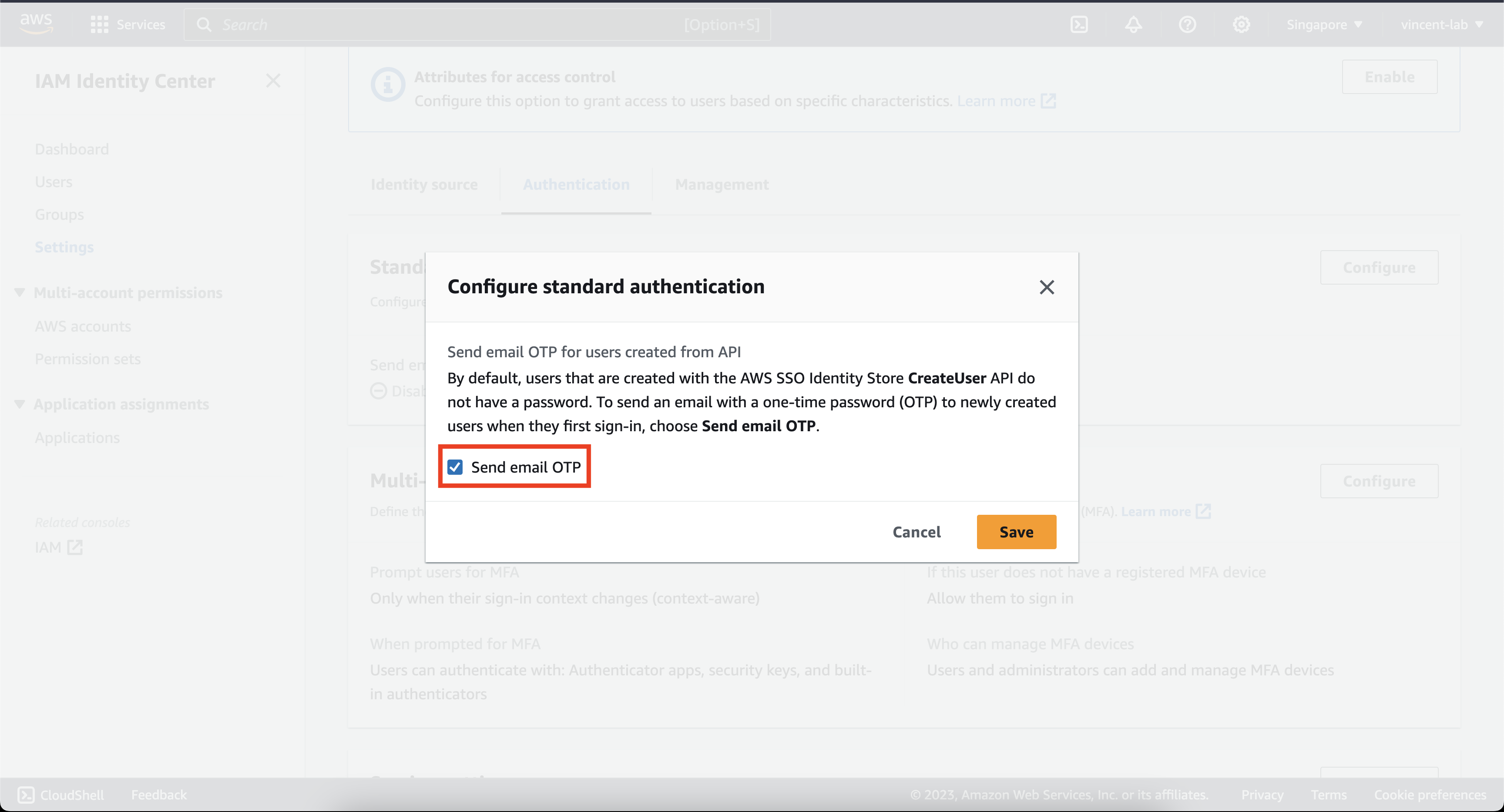
Click Configure on Standard authentication and then check the box on Send email OTP

Next click Configure on Multi-factor Authentication
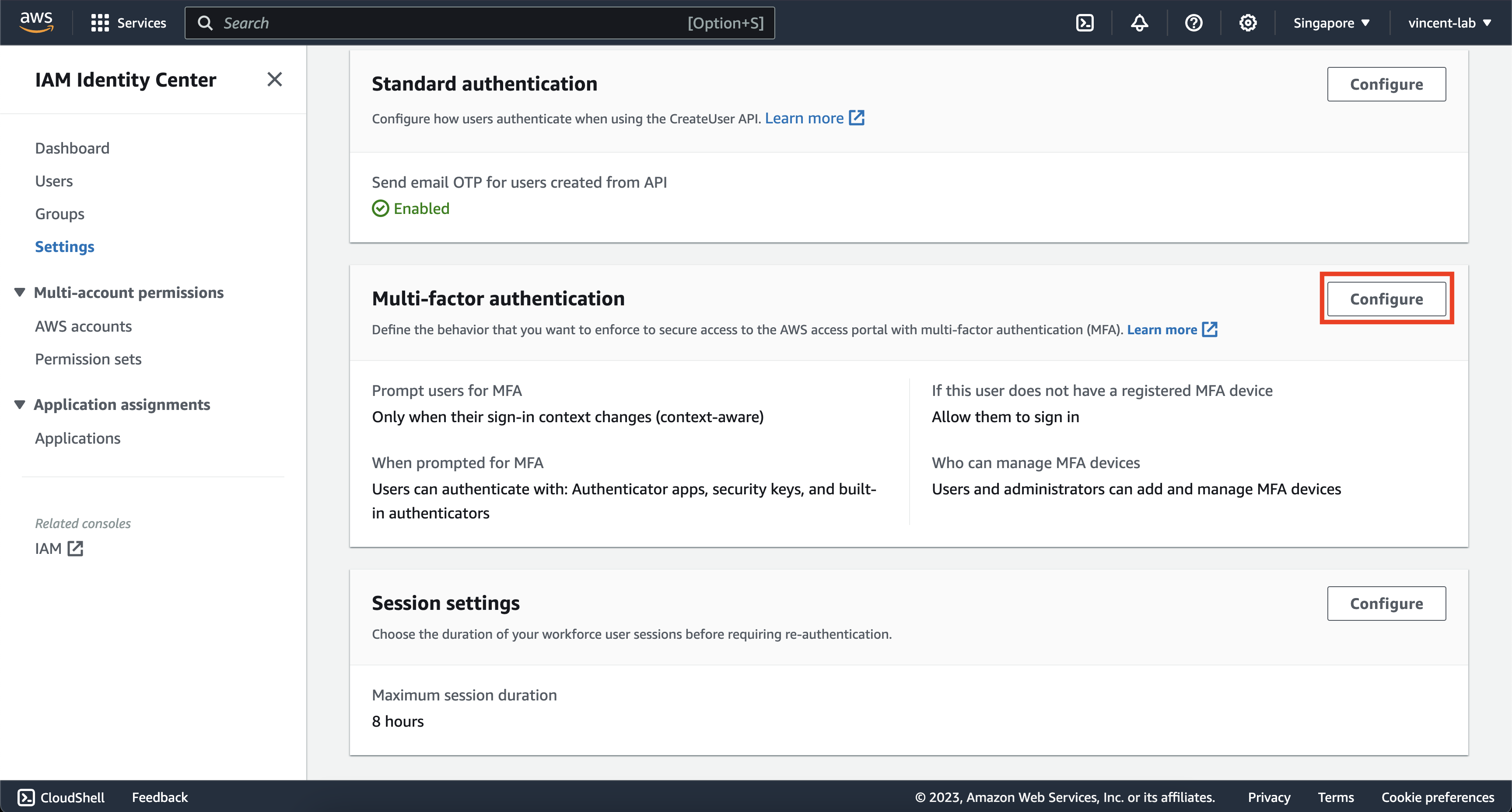
You can choose to be creative on this screen, but I would strongly advise that you copy the settings on the screen for maximum security. But you can be flexible between context-aware and always-on, as with anything on security, there's always a tradeoff between more secure and more comfortable, the more comfortable you are the less secure it is like not enforcing MFA.
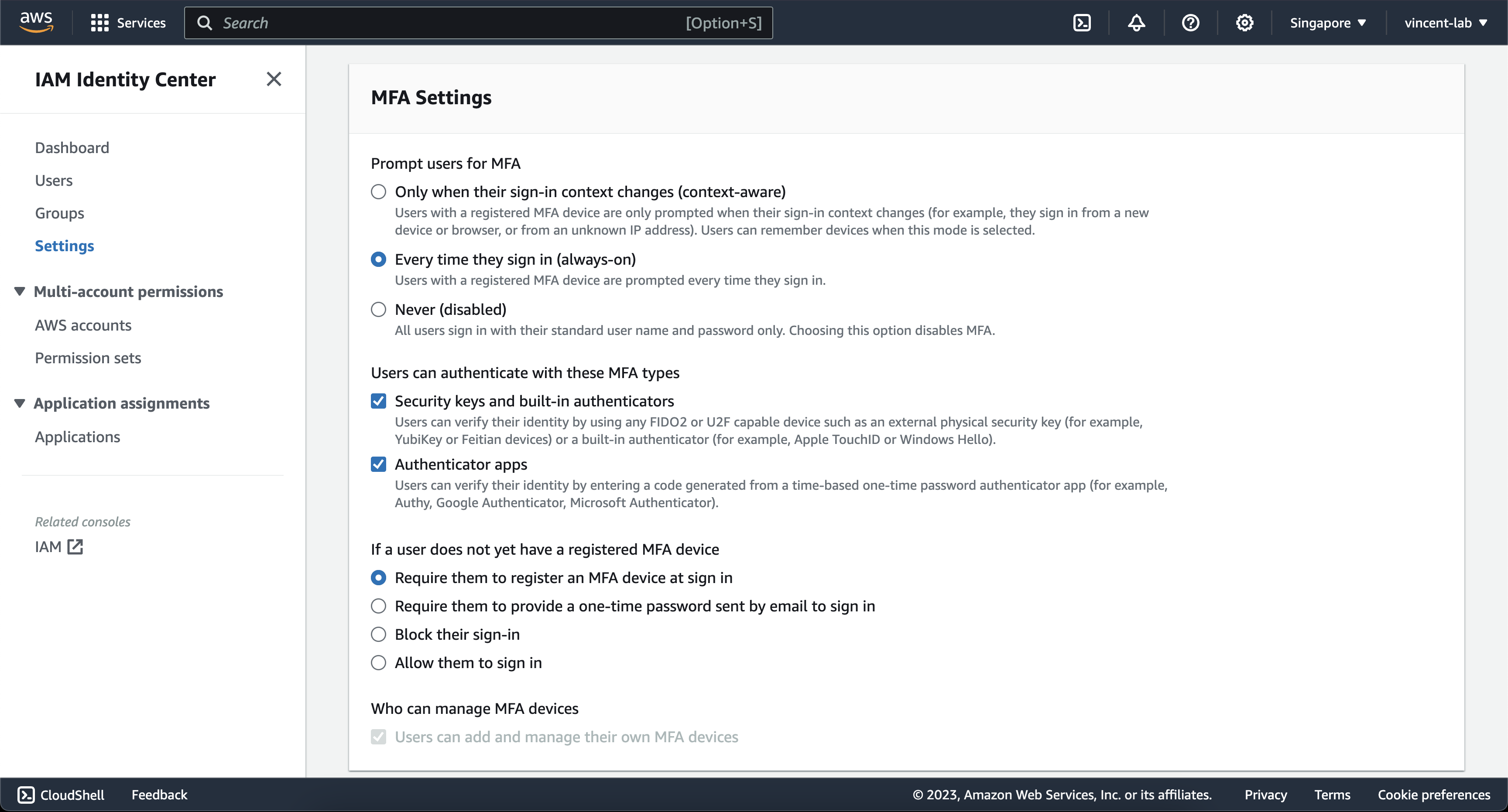
Note: to improve security even further, you can even choose to disable Authenticator apps and only enable Security keys if you have hardware devices such as Yubikey. But I will take the most common use-case and allow virtual authenticator
Creating permission sets and groups
Now comes the fun part setting up your users and permissions
Click on Create permission set

You can choose on one of the predefined permission set or create your own custom. But for this example I will be using the AdministratorAccess predefined permission set

Click on next

Feel free to fill it in or just leave it as the default value, both work. Then hit next and then hit create after you review that the information is correct.
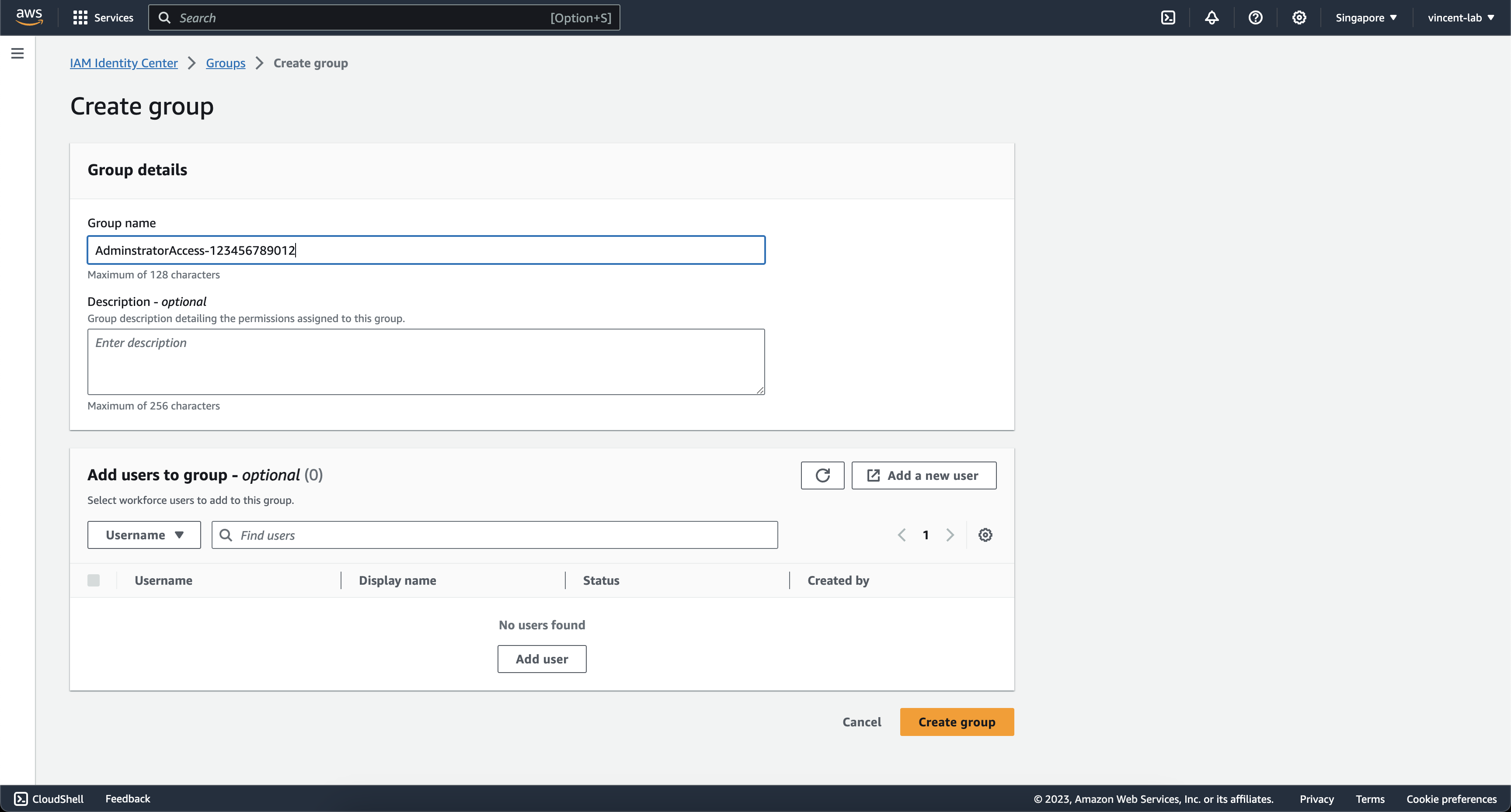
Next go to https://us-east-1.console.aws.amazon.com/singlesignon/home?region=ap-southeast-1#/groups
Create a group with the name of your permission sets with the accountId/accountAlias
Example AdministratorAccess-123456789012
Go to https://us-east-1.console.aws.amazon.com/iamv2/home?region=ap-southeast-1#/organization/accounts
Check the box for your AWS account and then click on Assign users or groups
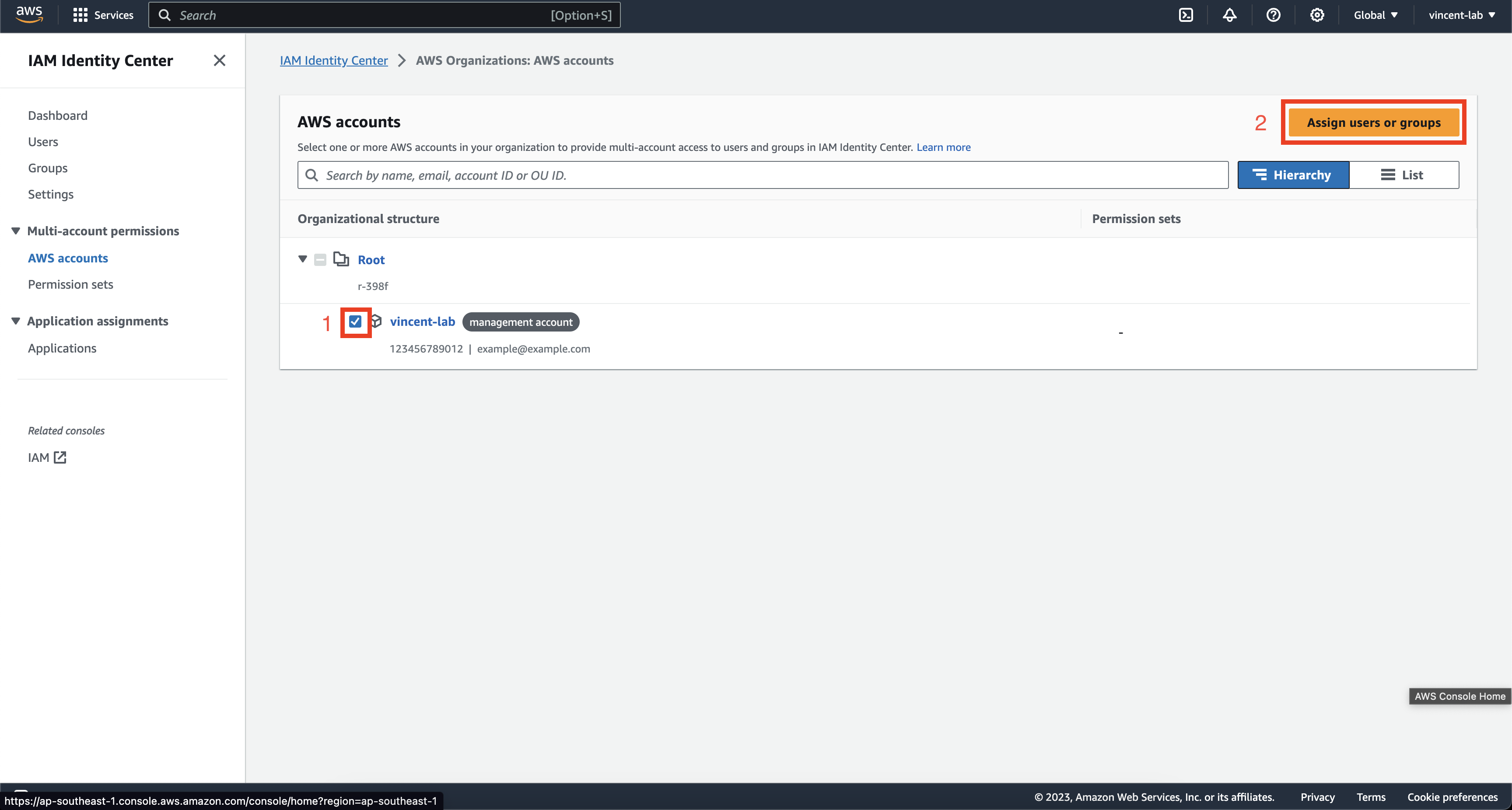
Check the box the group that we created earlier, then hit Next

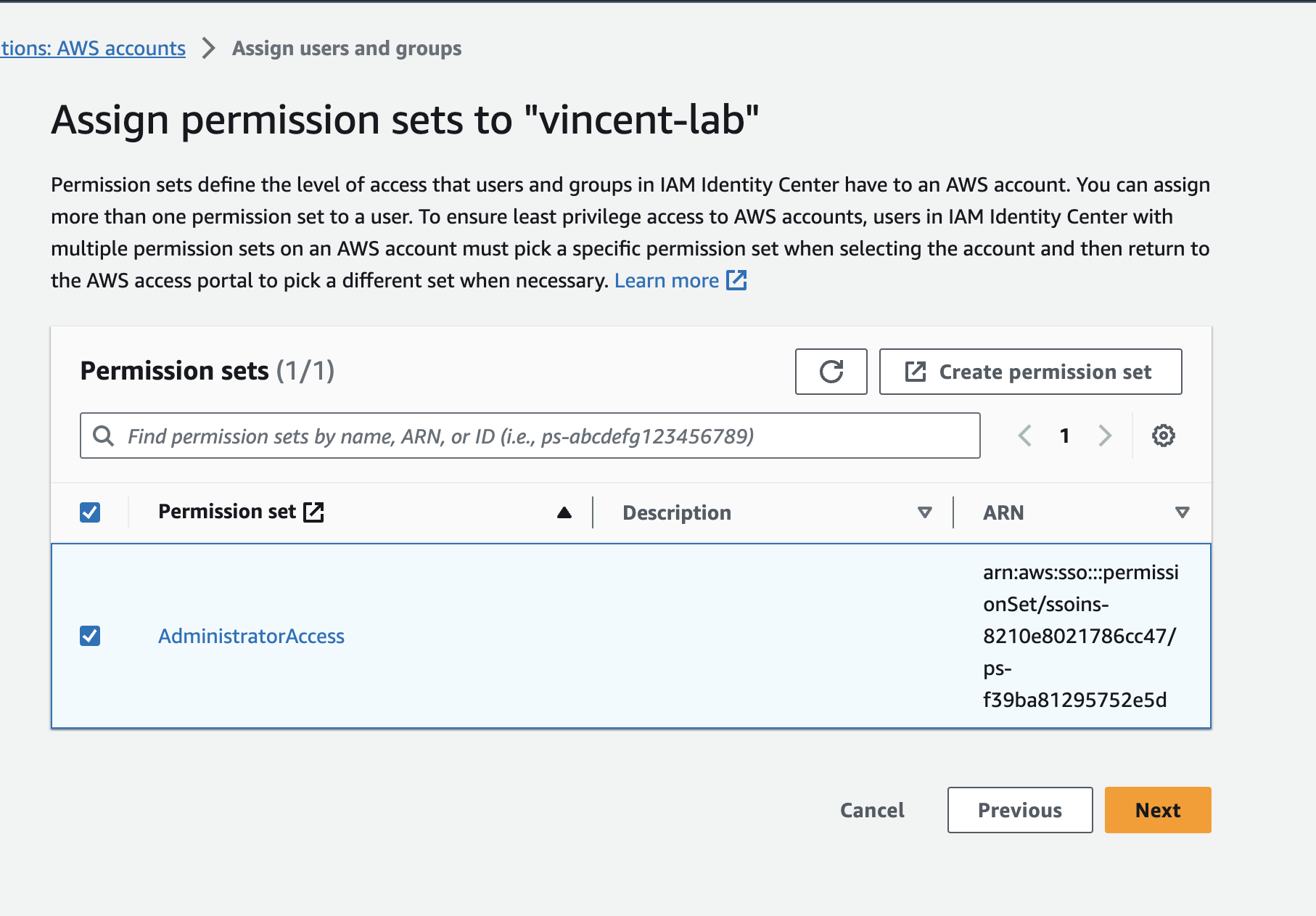
Same goes for the permission sets and hit Next and Submit once you reviewed that the information is correct.
Repeat the steps above for all the permission set you want to create
Creating the users and assigning them permissions
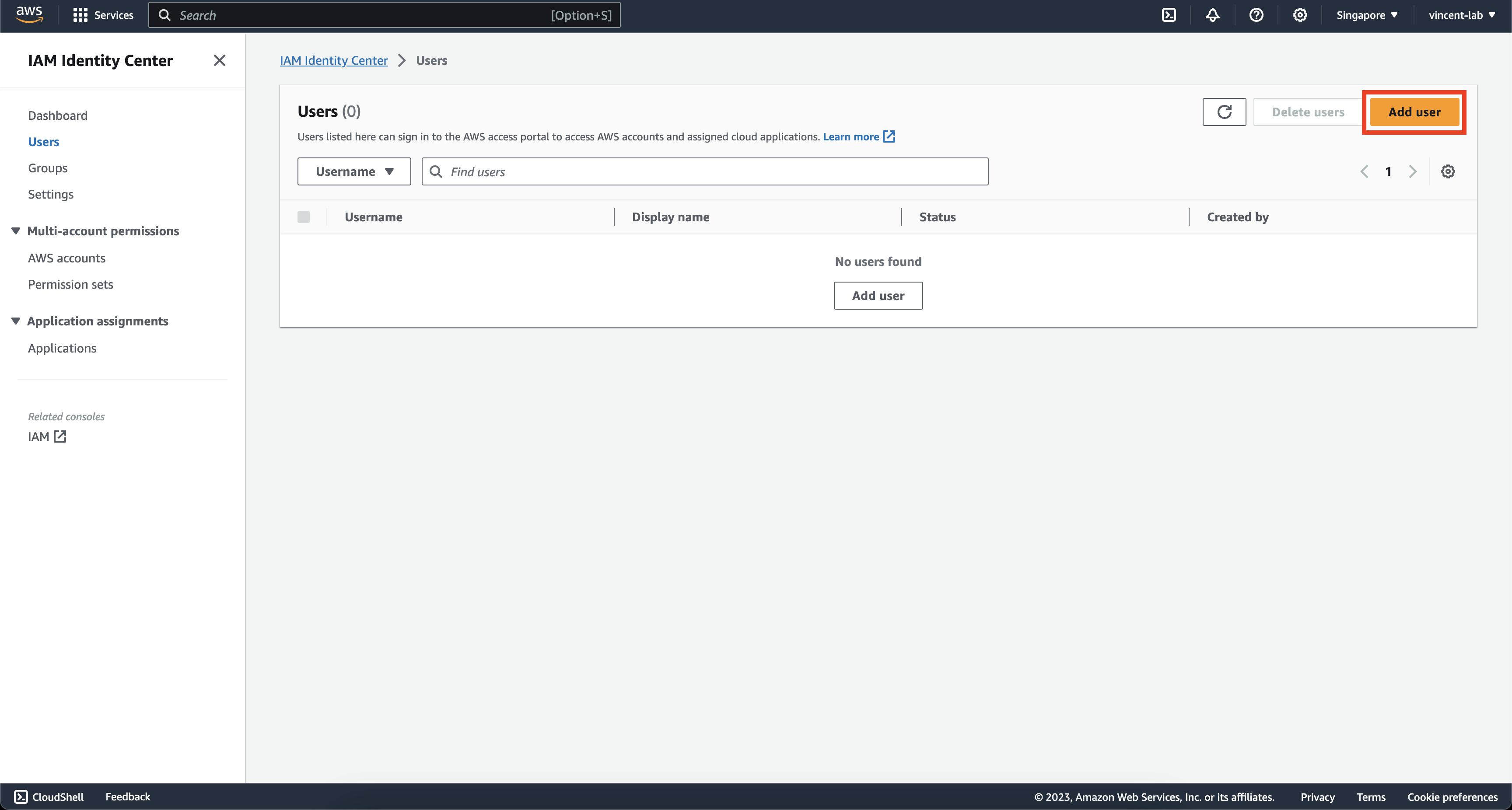
Next go to https://us-east-1.console.aws.amazon.com/singlesignon/home?region=ap-southeast-1#/users
Click on Add users
Fill in the details of user that you want to create, then hit Next

Assign the users to the groups that you have created, then hit Next

Review the info then click on Add user
Account Setup
Check the email that you have provided on the users, you should see an email similar to this

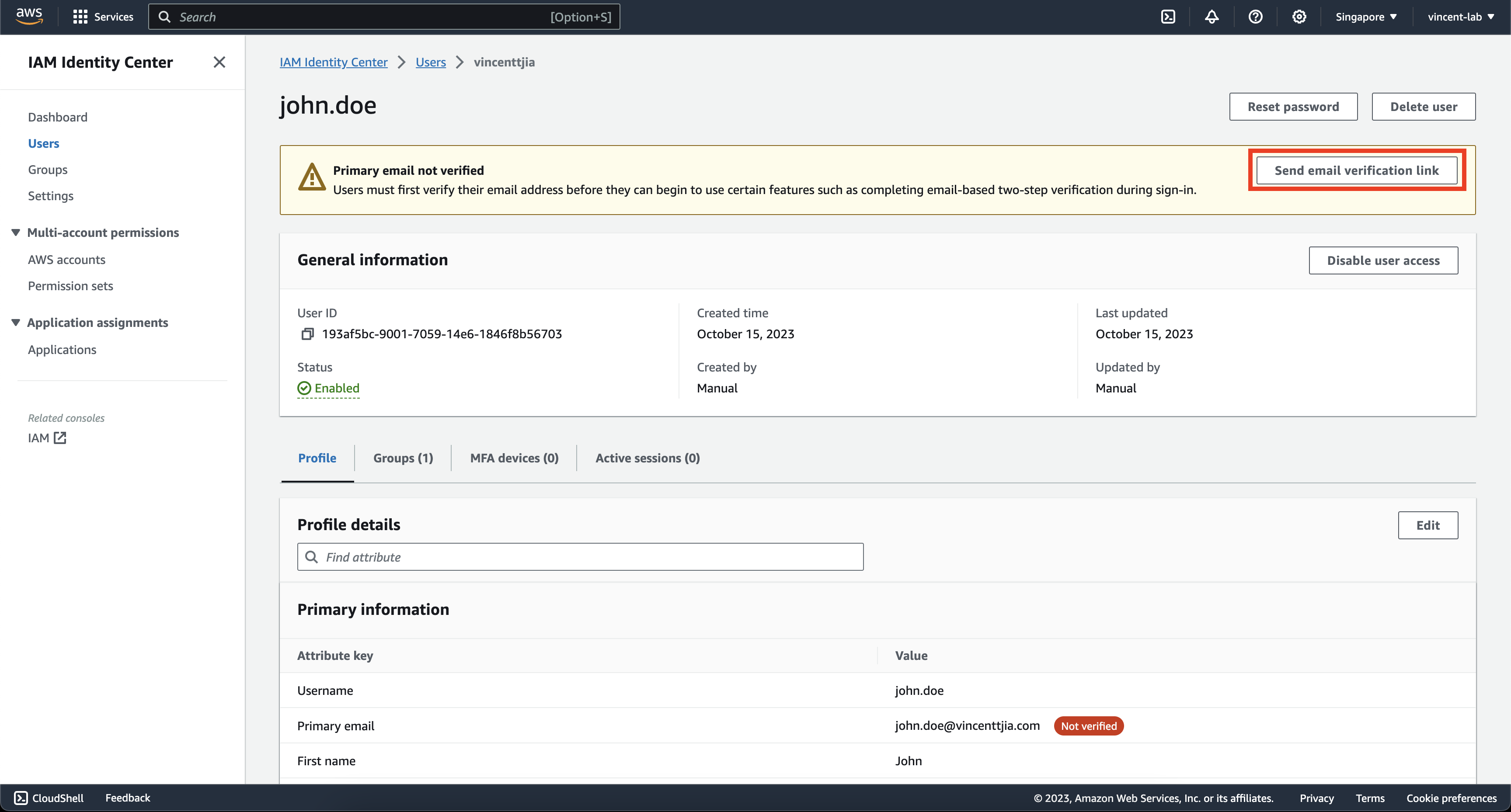
If for any reasons you did not receive the email, you can go to https://us-east-1.console.aws.amazon.com/singlesignon/home?region=ap-southeast-1#/users, click on the user and on the top of the page click on Send email verification link
Continue through the setup, by setting up your password and MFA.
Now, you should now be arriving at this page

Now that you have confirmed that you have access, we can start on setting up your temporary credential on the cli.
aws configure sso
SSO session name (Recommended): <You can choose any>
SSO start URL [None]: <Use the url from earlier>
SSO region [None]: <The region that was used earlier>
SSO registration scopes [sso:account:access]: <Just leave blank and hit enter>
Example
SSO session name (Recommended): personal
SSO start URL [None]: https://d-1234acd5.awsapps.com/start/
SSO region [None]: ap-southeast-1
SSO registration scopes [sso:account:access]:
Confirm and continue, then allow it
CLI default client Region [ap-southeast-1]: <Use which ever region best for you>
CLI default output format [None]: <Use which ever format best for you>
CLI profile name [SuperAdmin-198266650228]: default
Example
CLI default client Region [ap-southeast-1]: ap-southeast-1
CLI default output format [None]: json
CLI profile name [SuperAdmin-198266650228]: default
Note: only use the profile default if you only have 1 credential, if you have multiple like SuperAdmin, PowerUser etc. You can separate their naming and pass the --profile parameter every time you want to use them
Now you should be able to use temporary credentials on your terminal and periodically run aws sso login when your session runs out
aws sso login
Cleanup(important)
Cleanup on the root account
Now that everything is done, there are a few cleanup that we need to do
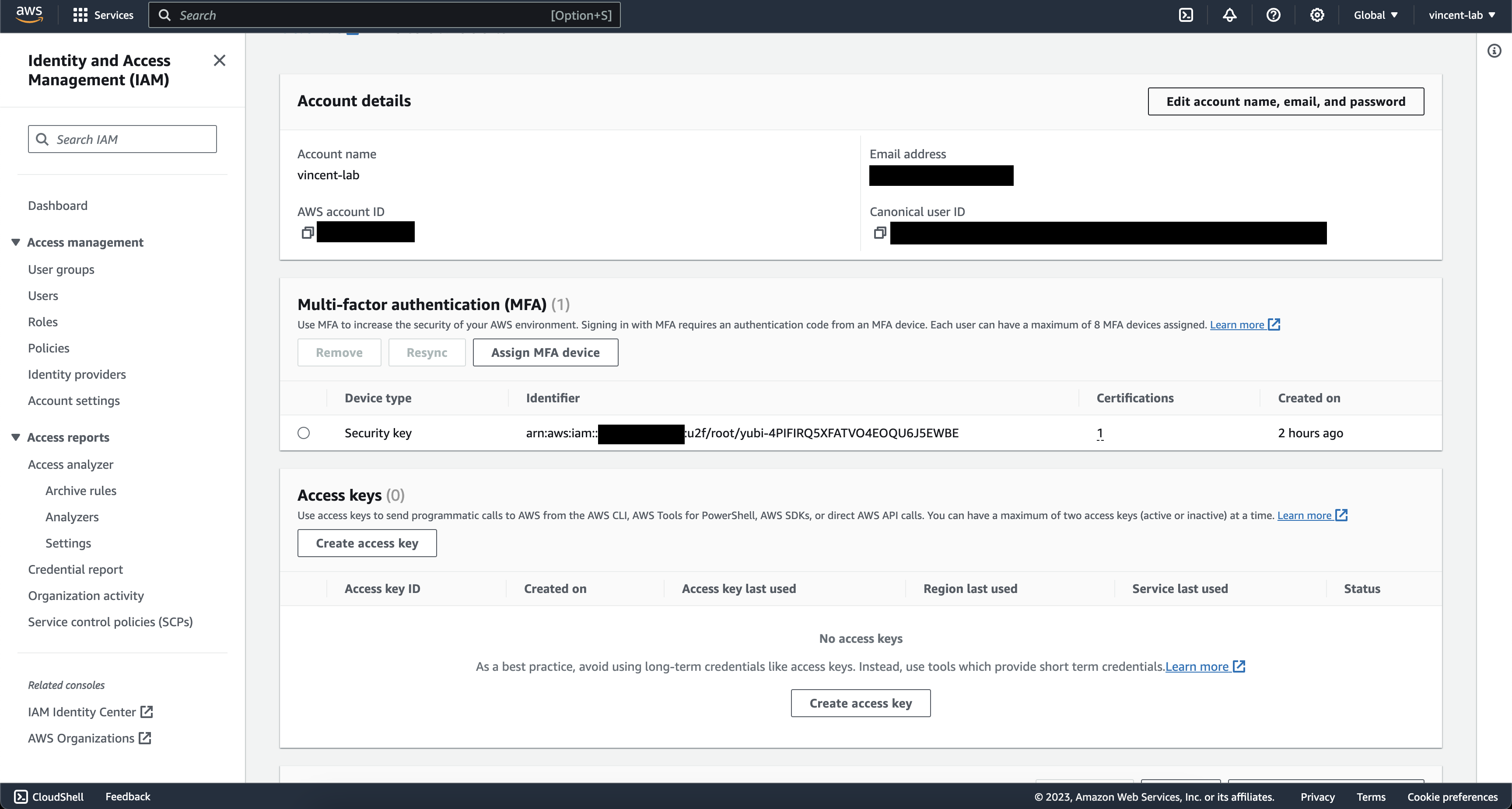
Go to https://us-east-1.console.aws.amazon.com/iam/home#/security_credential
Delete any root access keys that you might have found here. But, before deleting other access keys be sure that you are not using them for anything else or stuff will break.
Secondly, generate a strong password using your password manager for your root account and don't forget to set up MFA to make sure that the root account is never compromised. I would suggest at least a 128-character password with a letter, number and symbol.
There are 2 approaches that you can use, you can store the password in your password manager if you ever need to use the root account in the future or you can choose not to store it and just request a password reset anytime you need to access the root account. This needs to be taken with a grain of salt as you will need to secure and maintain access to the email that is associated with the root account as well.
Ideally, it should look like this
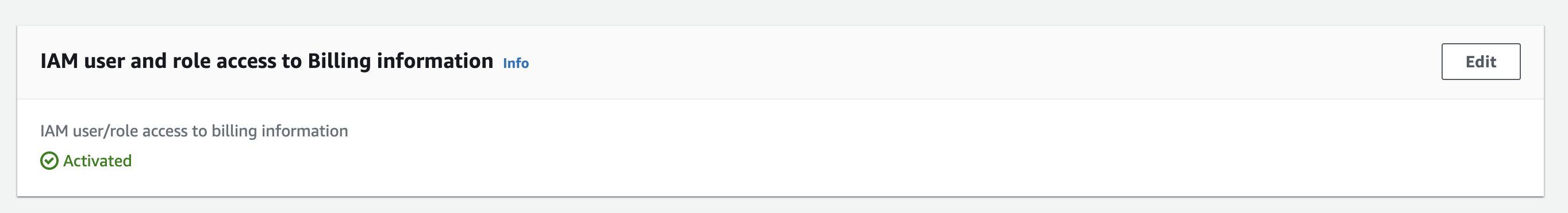
Lastly, as root, you would want to give access to Billing for yourself
Go to https://us-east-1.console.aws.amazon.com/billing/home#/account
then scroll down until you find IAM user and role access to Billing information edit it and activate IAM access
Cleanup on IAM Users
Delete all existing IAM users on your account, but before deleting please be sure that you have re-created the user in IAM Identity Center, assigned the correct permission and you have communicated it clearly to the affected user the new method to login and assume cli access.
Nice to have
Custom domain
You can set a custom domain for your AWS SSO login portal
Go to the settings page we visited earlier from https://ap-southeast-1.console.aws.amazon.com/singlesignon/home -> Scroll down to Identity Source -> Actions -> Customize AWS access portal URL

Troubleshooting
Running issue into assuming different profiles
If you only used the default profile you will not be running into this issue. But if you set up multiple profiles you might have issues such as running the terraform version before 0.12
I would suggest you install Granted-cli and then you can just do
assume profileName

